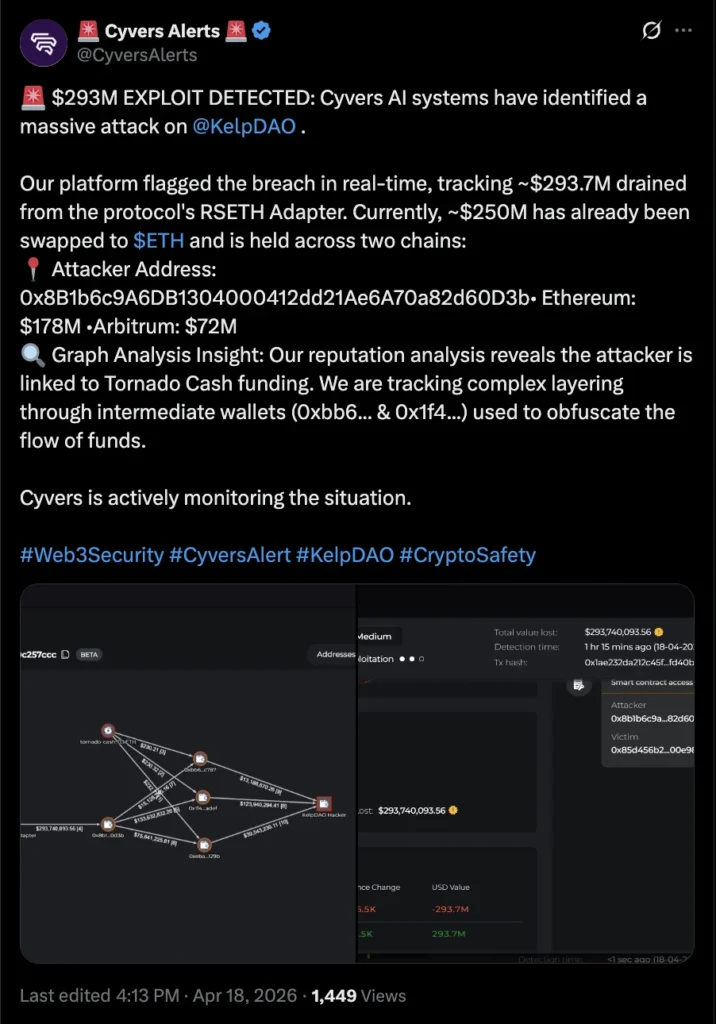
The decentralized finance (DeFi) ecosystem was once again rocked by a significant cybersecurity breach as Kelp, a prominent liquid restaking protocol, announced on Saturday that it had fallen victim to a sophisticated cyber attack. The exploit resulted in the immediate pausing of smart contracts governing its restaking token, rsETH, as the platform launched an urgent investigation into the incident. Early reports indicate that the attack led to the loss of approximately $293 million in user funds, underscoring the persistent and evolving threats within the rapidly growing digital asset space.
The Genesis of the Attack: Exploiting the rsETH Adapter Bridge
According to blockchain security firm Cyvers, the attacker specifically targeted and exploited the rsETH adapter bridge contract. This critical piece of software acts as the intermediary, managing the intricate interactions and cross-chain transfers of Kelp’s rsETH token. The vulnerability within this contract allowed the malicious actor to drain a substantial portion of the protocol’s assets.
Kelp confirmed the breach in a statement posted on X (formerly Twitter): "Earlier today, we identified suspicious cross-chain activity involving rsETH. We have paused rsETH contracts across mainnet and several Layer-2s." This swift action, while necessary to prevent further losses, has effectively halted all operations involving the rsETH token on the affected networks.
Unraveling the Attacker’s Footprint: Tornado Cash and ETH Conversion
Cyvers further detailed the attacker’s methodology and subsequent actions. Investigations revealed that the attacker’s wallet was funded through Tornado Cash, a cryptocurrency mixer known for its privacy-enhancing features, which can also be exploited to obscure the origins of illicit funds. This use of a mixer is a common tactic employed by cybercriminals to launder stolen cryptocurrency and make tracing the funds more challenging.
Following the initial exploit, the attacker moved with remarkable speed to convert a significant portion of the stolen assets. Approximately $250 million of the drained funds were reportedly converted into Ether (ETH), the native cryptocurrency of the Ethereum Layer-1 blockchain. This conversion to a more liquid and widely traded asset is a standard practice for attackers seeking to cash out their gains.
The Ripple Effect: AAVE Freezes rsETH Markets and Broader Protocol Exposure

The cascading impact of the Kelp exploit was immediately evident across the DeFi landscape. In response to the heightened risk, the decentralized finance lending platform Aave announced the freezing of rsETH markets on its V3 and V4 protocols. This proactive measure by Aave aims to protect its users from potential contagion and further losses stemming from the Kelp incident.
Cyvers also highlighted that at least nine other cryptocurrency protocols had exposure to the rsETH token. These platforms have also reportedly frozen activity related to the token on their respective services as they assess the full extent of their exposure and implement necessary safeguards. The interconnected nature of DeFi protocols, where assets and smart contracts often rely on each other, means that an exploit in one protocol can have significant ramifications for many others.
Expert Analysis: Composability and the Inherent Risks in DeFi
The Kelp exploit serves as a stark reminder of the inherent risks associated with composability in decentralized finance. Composability, the ability for different DeFi protocols to interact and build upon each other, is a core strength of the ecosystem, fostering innovation and efficiency. However, it also creates complex interdependencies that can amplify the impact of security vulnerabilities.
Deddy Lavid, CEO of Cyvers, commented on the incident, stating, "This is exactly the kind of incident that highlights the risks of composability in DeFi." This sentiment underscores the ongoing challenge for DeFi developers and security experts: balancing the benefits of interconnectedness with the need for robust security measures that can withstand sophisticated attacks.
A Troubling Trend: A Persistent Wave of DeFi Exploits
The Kelp attack is not an isolated incident but rather the latest in a disturbing string of high-profile cybersecurity breaches that have plagued the cryptocurrency industry in recent months. These exploits have collectively resulted in staggering financial losses, raising serious concerns about the security posture of many DeFi platforms.
Data compiled by various security analytics firms indicates a significant increase in crypto losses due to hacks and scams. For instance, reports suggest that Web3 hacks alone accounted for approximately $482 million in the first quarter of 2026, a figure that continues to grow with each new incident. This ongoing trend highlights a critical need for enhanced security protocols, rigorous auditing, and a more proactive approach to threat mitigation within the DeFi space.
Contextualizing the Threat: The Drift Protocol Hack

To further illustrate the scale of the problem, the Kelp exploit bears a resemblance to a similar, albeit slightly larger, incident that occurred in April. The decentralized cryptocurrency exchange Drift Protocol suffered an exploit that drained the platform of an estimated $280 million.
The Drift Protocol incident was particularly concerning as its post-mortem analysis revealed a meticulously planned attack. The Drift team reported that the exploit involved months of deliberate preparation, including the infiltration of their development team by individuals suspected to be North Korean state-affiliated hackers. In a detailed update, the Drift team disclosed that they had met the attackers at a major crypto conference and collaborated with them for several months. This collaboration ultimately allowed the attackers to deploy malware on developer machines, leading to the compromise of the platform. This case underscores the sophistication of some attackers and the potential for insider threats or social engineering to play a role in these breaches.
Broader Implications for the DeFi Ecosystem
The repeated and substantial losses from DeFi exploits have several significant implications for the broader ecosystem:
- Erosion of Investor Confidence: Frequent security breaches can severely damage investor confidence in DeFi. Users may become hesitant to deposit their funds into protocols perceived as vulnerable, hindering the growth and mainstream adoption of decentralized finance.
- Increased Regulatory Scrutiny: The financial scale of these exploits is likely to attract increased attention from regulators worldwide. This could lead to the implementation of stricter regulations, which, while potentially enhancing security, might also stifle innovation or increase compliance costs for legitimate projects.
- Demand for Enhanced Security Audits and Best Practices: The ongoing attacks are fueling a greater demand for comprehensive and independent security audits. Protocols are under pressure to adopt more stringent security practices, including rigorous code reviews, penetration testing, and bug bounty programs, to identify and rectify vulnerabilities before they can be exploited.
- Innovation in Security Solutions: The persistent threat landscape is also spurring innovation in cybersecurity solutions tailored for blockchain and DeFi. This includes advancements in smart contract auditing tools, real-time threat detection systems, and cross-chain security protocols.
- Focus on Decentralized Insurance: The possibility of covering losses from hacks and exploits through decentralized insurance mechanisms is likely to gain further traction. Such solutions could provide a financial backstop for users and protocols in the event of a breach.
Looking Ahead: A Call for Vigilance and Robust Security
The Kelp protocol attack, with its substantial financial implications, serves as a critical juncture for the DeFi industry. While the investigation into the specifics of this exploit is ongoing, the incident reiterates the paramount importance of robust security measures, continuous vigilance, and a proactive approach to cybersecurity. As the DeFi space continues to evolve and attract more capital, the battle against sophisticated cyber threats will undoubtedly remain a defining challenge. The industry’s ability to adapt, innovate, and implement effective security strategies will be crucial in building a sustainable and trustworthy decentralized financial future.
Kelp has yet to provide a detailed timeline for the resolution of the issue or plans for fund recovery. Cointelegraph reached out to Kelp for comment but had not received a response by the time of publication. The situation remains fluid, and the DeFi community will be closely watching for further updates and the eventual implications of this significant breach.